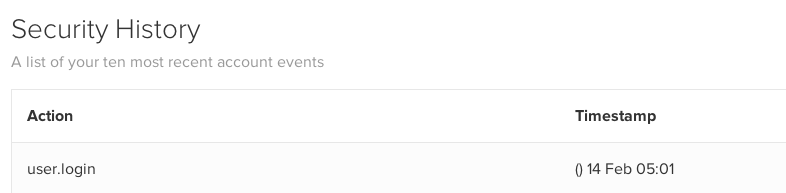
The “snippet preview” functionality of the Yoast Wordpress SEO plugin was susceptible to cross-site scripting in versions before 2.2 (<= 2.1.1). This vulnerability appears to have been reported 2 years ago by someone named “badconker”, but the plugin author said that it was already patched. Unfortunately, it appears that this is not the case. If you are running this plugin, I recommend updating to the latest version .
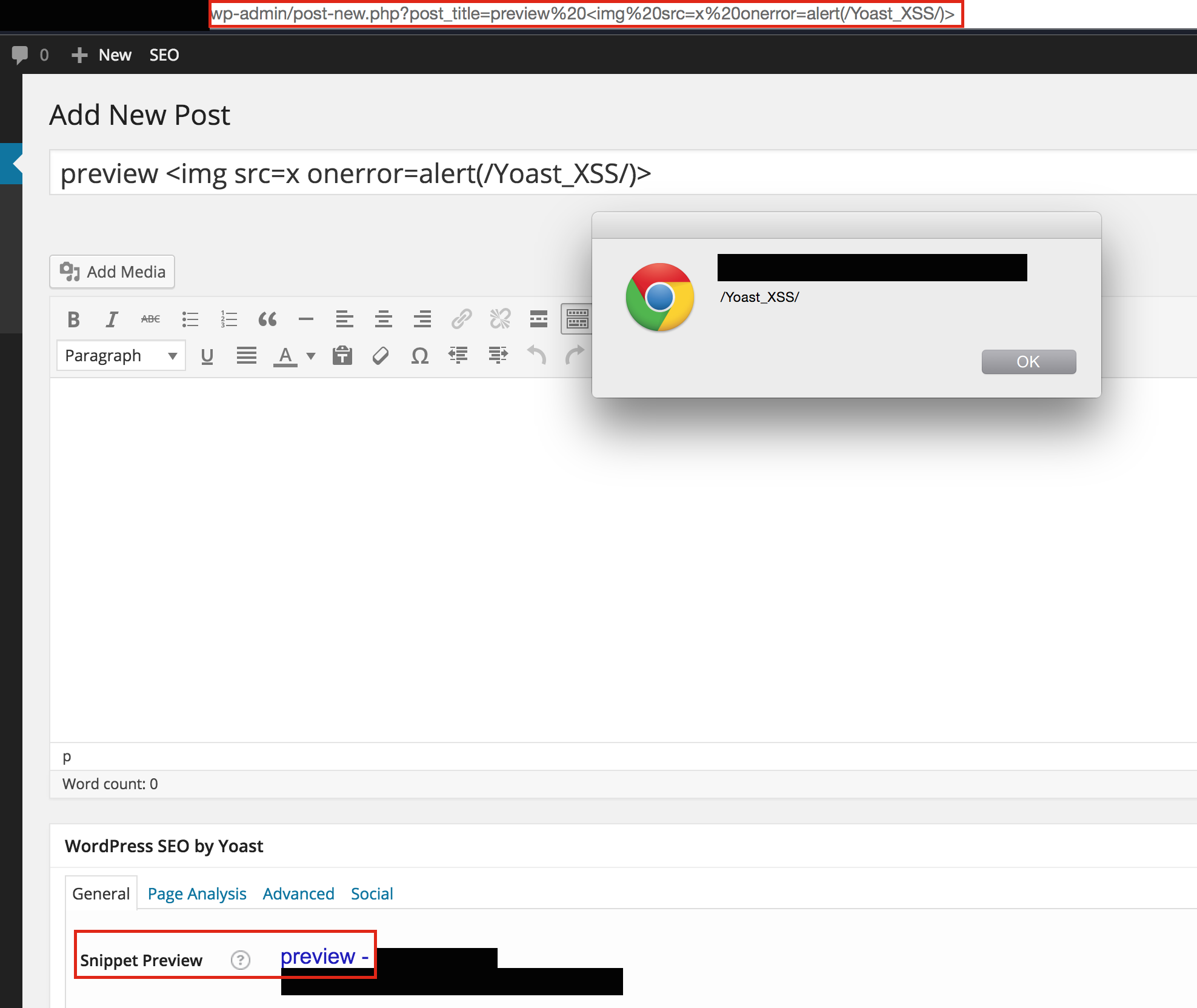
Yoast Wordpress SEO XSS in action